Data Privacy Day 2018: How safe is your personal information?
Personally Identifiable Information, commonly referred to as PII, can be broadly defined as any data that could potentially identify a specific individual. Additionally, it may include any information that can de-anonymize a person from other persons or a set of anonymous data.
PII has grown immeasurably in both accessibility and context since its origins in the mid 1970s. Once upon a time, PII resided on computers physically sitting in secure rooms and might come in the form of a person’s name, address, date of birth, social security number or even a organization’s customer identification number. Today, PII undoubtedly sits in the cloud and on user devices (arguably in IoT) everywhere making it easily accessible from virtually anywhere. Moreover, smartphones and sensors provide new measures that when captured and stored may qualify as PII. This data may be relative information, such as a user’s location or power consumption or uniquely identifiable biometric information, like a user’s fingerprints, 3-D face scans, voice prints or gait to name a few. Often unbeknownst to users, 3rd parties access and process this data with some going so far as to sell it in a muli-billion dollar industry.
To help illustrate what makes up PII Kalki Consuliting provides this helpful infographic: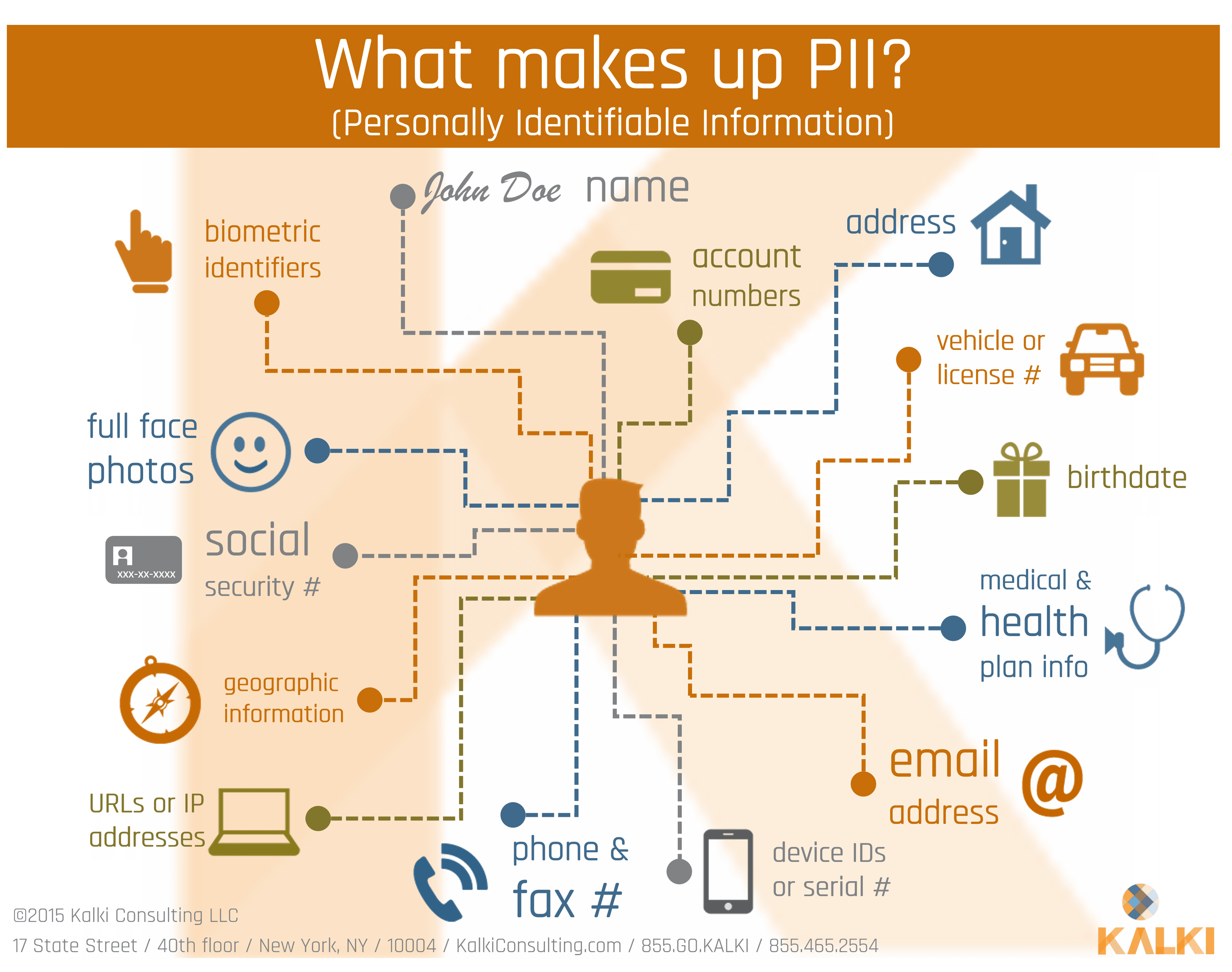
So back to the question, “Where’s your PII?” The answer: practically everywhere including the most powerful and vulnerable places – smartphones. Practically always on and in the proximity of a user, smartphones have access to email, phone calls, homes, automobiles and possibly even employer assets. Not to mention these personal devices track and record practically every movement, sound and sight accessible to the device’s sensors, a.k.a. Data in Vicinity. This can include the PII of other individuals near the device and occur wherever the device may be: at home, at work or elsewhere. A smartphone may provide a slew of additional information including a user’s insights, health and financial data as well as a user’s personal activities. Unlike data centers designed for security, smartphones hold highly confidential information without the security benefits of fences, guarded doors or any kind of physical locks. The physical security of a smartphone might consist of a “strong” passcode (possibly an ill advised fingerprint) easily accessible remotely through a number of radio frequencies (RF). These characteristics and the insatiable appetite for data by marketers, governments, cyber criminals and even employers as well as their competitors combine to make smartphones extremely lucrative targets as they can unlock so much information and insight. And with more data desired by more parties in more locations with lesser guards, the compromise of one’s PII seems inevitable.
So what to do - avoid smartphones? While an available, strong proactive measure, this is not a practical option for most people or businesses. Soon though, the very valuable PII may serve as the catalyst in protecting user identity and other valuable data through a technique the U.S. Department of Information System Agency (DISA) calls Continuous Multi-Factor Authentication (CMFA). In this approach the strong correlation of multiple forms of PII qualified behavioral data, which is both strongly associated to a user AND able to be continuously monitored by a mobile device, will authenticate the device’s user for authorized access.
Until then be aware, keep informed and stay on alert. Additionally, here is a list of 10 tips currently available to protect PII and help guard data privacy on smartphones:
- Check and configure app privacy settings.
- Use a strong password that auto locks after sitting idle and avoid using biometrics.
- Encrypt the device storage.
- Enable remote location and device-wiping.
- Utilize a reputable mobile security solution.
- Be mindful of the apps you download and understand the permissions requested and used.
- If you don’t use it – lose it. Delete apps not in use. Turn off Bluetooth when not in use.
- Avoid free or unsecured WiFi access.
- Refrain from clicking any links received via text or email – including messages sent from a trusted source – unless you are expecting the link.
- Install system and app updates to maintain the most current operating system for the smartphone.
AND LASTLY as a bonus tip for tablets, laptops and desktops:
- Use a webcam cover
This mobile security blog post was inspired by Data Privacy Day (a.ka. Data Protection Day in Europe ), which is celebrated on January 28th of each year by the United States and some 49 countries. The holiday commemorates the January 28th 1981 signing of Convention 108: the first legally binding international treaty dealing with privacy and data protection. Championed by the National Cyber Security Alliance, Data Privacy Day focuses on raising awareness among businesses and users on the privacy and data protection of personal information online. The audience today includes families and consumers in its educational efforts as the cause has expanded its initiatives to encourage compliance with privacy laws and regulations, create dialogues among stakeholders and promote activities that encourage individual control over PII.
Editor's Note: This post was originally published in January 2018 and has been updated for accuracy and comprehensiveness.